SEC Cybersecurity Disclosure Rules
Final Rule on Cybersecurity Risk Management, Strategy, Governance, and Incident Disclosure by Public Companies
Why This New SEC Cybersecurity Rule?
Cybersecurity threats and attack surfaces continue to grow as more data moves to the cloud. It’s important for companies to maintain clear and consistent processes and policies to protect their data and the systems, applications, and networks that contain it.
Cybersecurity posture and material breaches impact the safety of shareholders’ investments in affected public companies, just like any other material changes or weaknesses that must be disclosed under existing SEC mandates.
In the words of the SEC…
“In our disclosure-based regime, investors have a right to financial statements prepared in accordance with Generally Accepted Accounting Principles (GAAP).”
– Assessing Materiality, March 2022
The new final rule extends this right to cybersecurity posture and material cybersecurity incidents.
When is the SEC Cybersecurity Rule Effective?
The rule was approved on July 26, 2023 and is effective as of December 18, 2023. Smaller reporting companies must comply as of June 15, 2024.
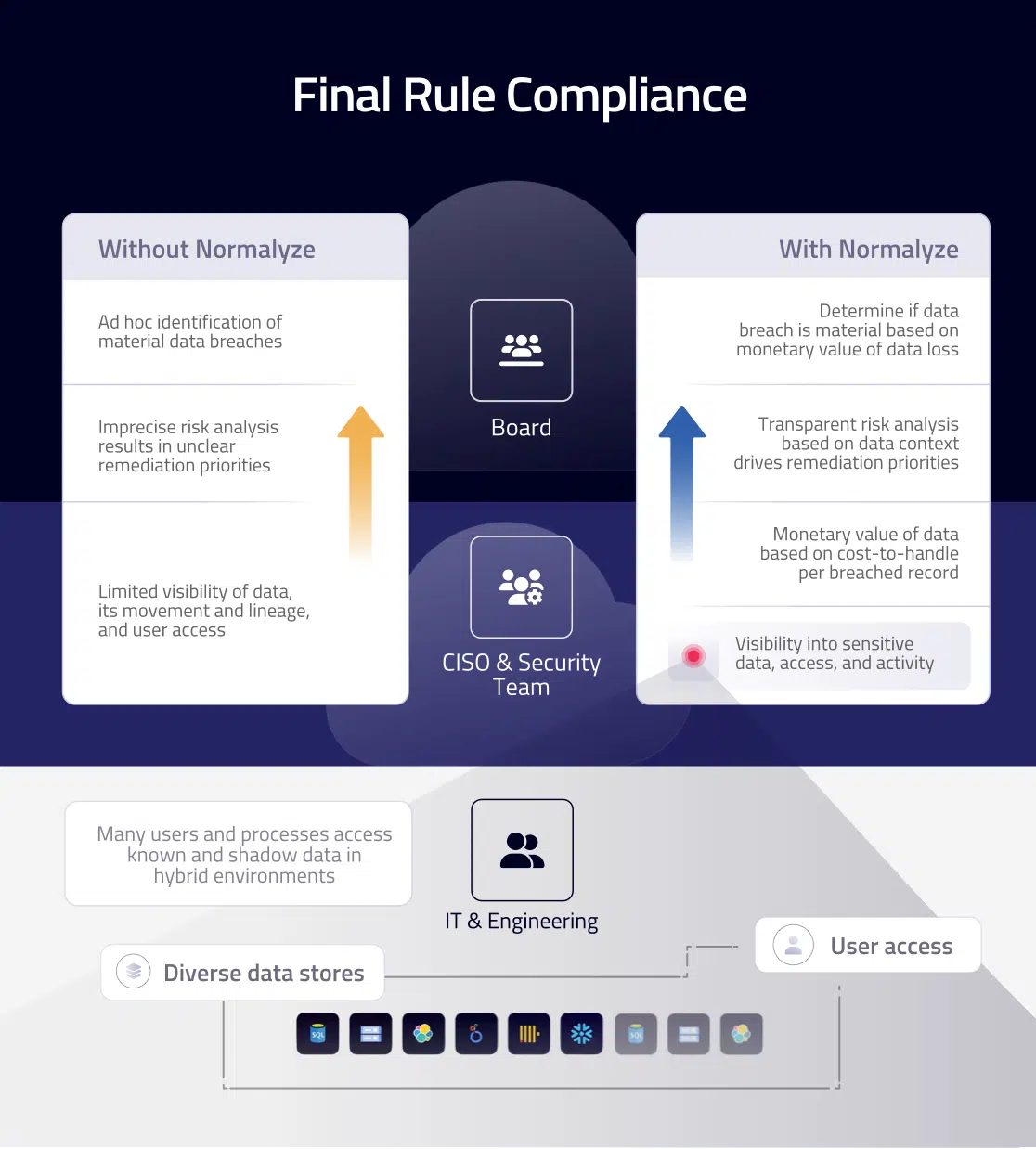
 What the New SEC Cybersecurity Disclosure Rule Means for Public Companies and How Normalyze Helps
What the New SEC Cybersecurity Disclosure Rule Means for Public Companies and How Normalyze Helps
Requirement 1: Annual Disclosure
Annually disclose material information describing a public company’s cybersecurity risk management, strategy and governance.
Get continuous visibility and control of security posture.
- Discover and classify data across your entire hybrid infrastructure.
- Identify over-provisioned users and roles and enforce the principle of least privilege.
- Initiate remediation of top-priority issues based on transparent risk analysis.
- Continuously monitor regulatory compliance.
Communicate and report on security posture clearly and transparently.
- Communicate posture improvement to executives and board members in terms of the cost of a potential breach.
- Report data security posture based on up-to-date status.
Requirement 2: Material Incident Disclosure
Disclose within four business days on SEC Form 8-K “any cybersecurity incident they determine to be material and to describe the material aspects of the incident’s nature, scope and timing, as well as its material impact or reasonably likely material impact on the registrant.”
Assess the financial impact of breaches and potential loss.
- The monetary value of data effectively communicates breach impact to executives and board members. Use calculations based on real-world data or customize to the specifics of your environment.
Monitor data for faster response and to limit the damage of breaches.
- Dynamic data visualization helps flag breach conditions early.
Incident Disclosure Timing
When does the four-day clock start ticking?
Assume a company discovers and confirms a cyber incident occurred on August 7. This does not mean disclosure must automatically occur four business days later. First, there’s an exception for cases of national security or public safety, as determined by the US Attorney General. In other cases, the trigger point is a company’s determination that the incident was material. The SEC defines material as if “there is a substantial likelihood that a reasonable shareholder would consider it important.” So, if materiality was determined two weeks after the discovery, on August 21, that’s when the four-day clock starts ticking.
In this scenario, the disclosure must occur within four business days, by August 25.