IaaS & PaaS: DSPM protects public clouds
 “…More than half (59%) of respondents believe that more than 30% of their organization’s sensitive data residing in IaaS and PaaS environments is insufficiently secured.” Cloud Data Security Report, 2023
“…More than half (59%) of respondents believe that more than 30% of their organization’s sensitive data residing in IaaS and PaaS environments is insufficiently secured.” Cloud Data Security Report, 2023
Protecting
sensitive cloud-resident data
What DSPM
provides in laaS/PaaS
data stores
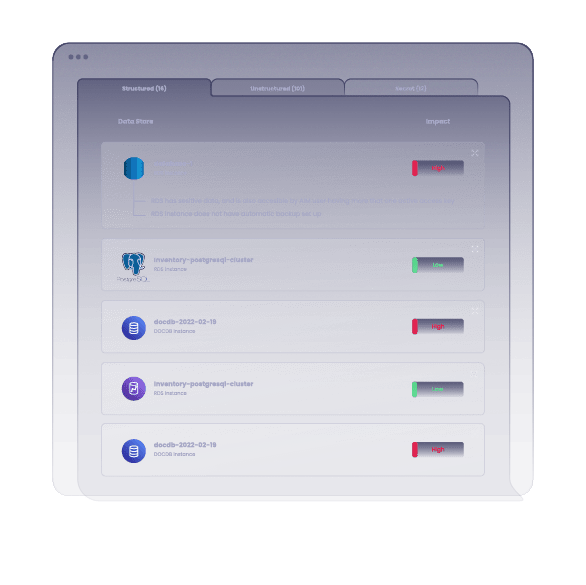
1 | Data discovery |
| Answers the question, “Where are my data?” A platform must discover cloud-native structured and unstructured data stores such as block storage and PaaS. |
2 | Data classification |
| Tells you what kinds of data exist and if they are sensitive (e.g., GDPR, PCI DSS, HIPAA). Answers questions like “Who can access my data?” and “Are there shadow data stores?” |
3 | Access governance |
| Ensures that only authorized users are allowed to access specific data stores or types of data. DSPM’s access governance workflows will also discover related issues, such as: “Are there abandoned databases?” or “Are there excessive privileges?” |
4 | Risk management |
| Detects potential attack paths that could lead to a breach of sensitive data. Detection includes vulnerabilities affecting sensitive data and insecure users with access to sensitive data. All this points teams to steps for remediation. |
How siloed point
solutions fall short
Subsets of DSPM’s functionality are seen in current and emerging tools for cloud data security. Unfortunately, their functionality is siloed, and these standalone tools do not fulfill all five major functions of DSPM required for systematic, comprehensive, and effective security of all cloud data.
Whether it’s Azure cloud security posture management, GCP data loss prevention, AWS data lake security, or Snowflake data governance features, there are significant limitations in relying on a single, siloed service for all your DSPM needs in multi-cloud environments.
The matrix below shows how current cloud security tools only partially address the five functions of DSPM in various types of cloud data stores. Essentially, DSPM fulfills all the squares stating “None” and may replace tools in the other squares –especially if an organization’s use cases for particular tools are minimal. Alternately, if an organization has significant investment in particular cloud security tools (such as populating a CMDB with hundreds of thousands of assets, owners, business criticality, etc.), the DSPM platform can also ingest operational data, alerts, and other metrics from your existing infrastructure of corresponding tools for security, IT operations, and DevOps. For use cases like data discovery and classification, access governance, compliance, or risk management measures, DSPM offers the widest range of flexibility for cloud data security.