Mergers and Acquisitions Data Security
Ensure a seamless security transition during M&A
Normalyze streamlines data security during the hectic M&A process, whether you’re merging, acquiring, or spinning off a business unit.
 Fast Posture Assessment
Fast Posture Assessment
Announcing a merger or acquisition makes you a target for cybercriminals seeking vulnerabilities. During M&A, agility is crucial for security teams and CISOs to navigate the increased risk.
Plug the Knowledge Gap
Merged security teams need to get a handle on a lot of information very quickly.
-
Data Discovery
Get a common understanding of systems and data, especially where sensitive data resides. Discover and classify data across your entire hybrid infrastructure.
-
Data Access
Get a simple, accurate view of access privileges for all cloud data stores. Identify over-provisioned users and roles and enforce the principle of least privilege.
-
Compliance
Continuously monitor regulatory compliance across multiple regulations and identify which controls are being missed.
-
Risk
Assess the security posture of merged infrastructure. Initiate remediation of top-priority issues based on transparent risk analysis.
-
Threats
Identify unauthorized access to data. Dynamic data visualization helps focus teams on quick response to attacks.
One Source
of Truth
A Complete View
- Using Normalyze, everyone sees the same complete set of data, risks, access, threats, and compliance posture, so conversations are fact-based and easier to discuss and analyze. Drill-down into data and risk detail ensures that teams can understand at whatever level of detail they need. The transparency of the solution ensures that all teams can trust the data and discuss issues from a common understanding.
Shared Duties,
Shared Success
Team Alignment
- Communication within the team is clearer with a complete, shared picture of the environment. Teams understand better what the issues are, and can agree and work to resolve them, even if they are different (and stricter) requirements than before the merger.
- M&A often involves the movement of large amounts of data from the systems of the acquired company to the systems of the acquirer. This data shift can cause security risks, so the teams need to work together to make it happen securely.
 The “Lean Team” Challenge
The “Lean Team” Challenge
M&A can lead to staff reductions in IT security, or add responsibility for the acquired infrastructure to existing teams.
The Big Picture
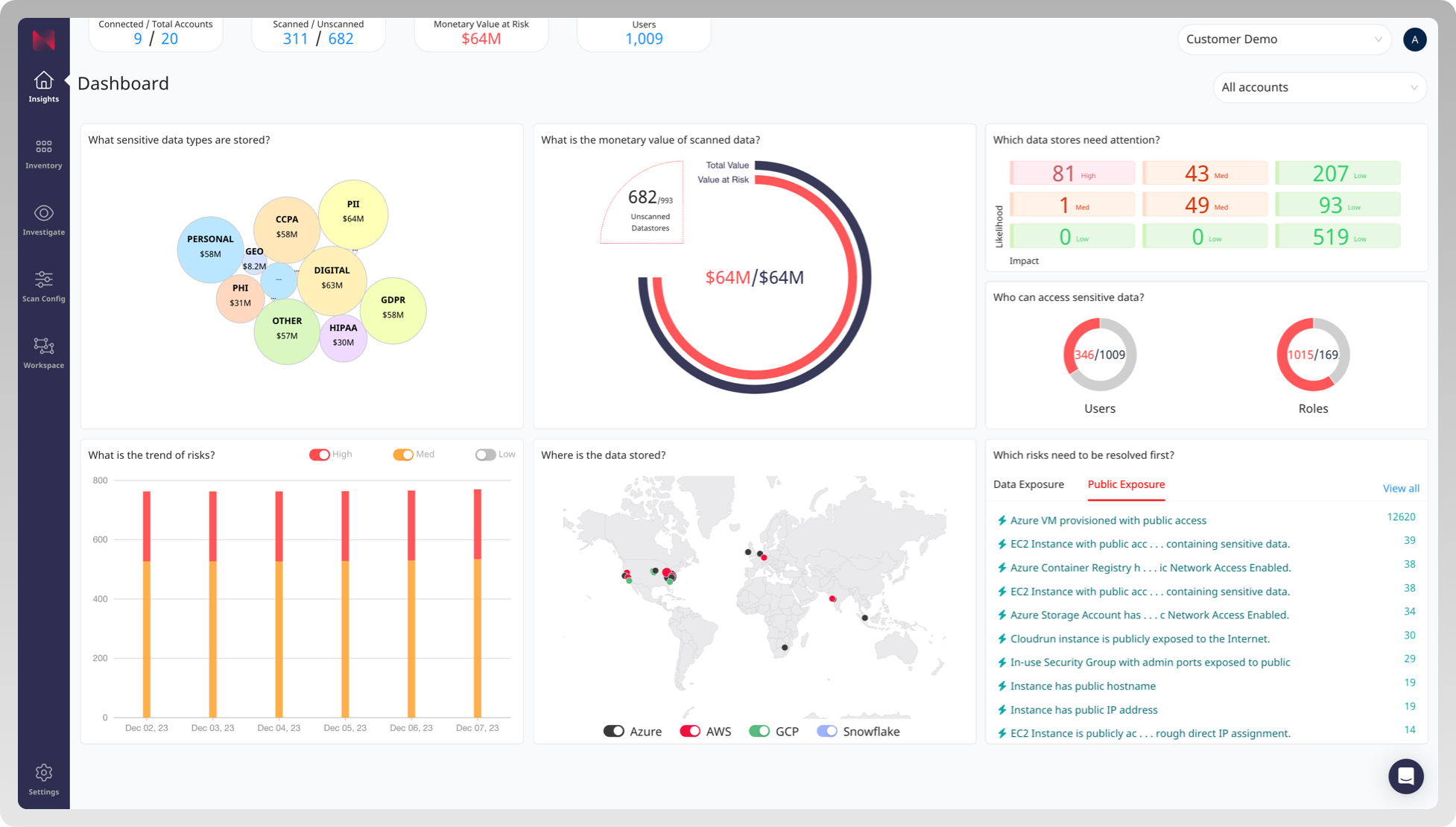
The Normalyze data security management platform provides an easy-to-understand integrated dashboard, visualizing the infrastructure and its data risk posture.
Security teams can view the location and sensitivity classification of all data stores across infrastructure-as-a-service (IaaS), platform-as-a-service (PaaS), software-as-a-service (SaaS), and on-premises environments. For deeper inspection, drill down into infrastructure and risk detail from all graphs and data in the dashboard.
Tackle the
Titans First
Business Impact
- Normalyze prioritizes risks based on a combination of the severity of the risk and the monetary value of the data at risk. This allows the security team to focus their energies on issues with the greatest business impact to the organization.
- With data classification based on risk profile and type of data, risk filtering by risk type and compliance tags, and other robust capabilities, smaller security teams continue to prioritize effectively.
Automate to Compensate
Operational Efficiency
- Startup is easy and fast. A simple process onboards cloud accounts via CloudFormation (AWS), Onboard script (GCP) or Terraform and typically completes in a few minutes.
- Normalyze only seeks the minimum permissions required in your cloud accounts and creates modular roles that minimize scope of permissions to specific product capabilities being enabled.
- Out-of-the-box integrations with third-party ticketing, notification, and automation platforms help security operators collaborate with DevOps and platform engineering teams to remediate risks in a timely manner. Normalyze provides security engineers with detailed, AI-generated instructions to perform guided remediation.
 Working Together for Success
Working Together for Success
Speak the Same Language
Communication is crucial
- By offering a common platform, Normalyze ensures that everyone is updated on vulnerabilities, changes, or incidents. This helps teams adapt to unfamiliar policies, practices, and politics; work with strangers from different corporate or even national cultures; and report to new bosses who may know nothing about your track record or ambitions.
- For security team members, the Normalyze dashboard showcases data risks, security scorecards, and trend analysis, making it easier to show progress made quarter over quarter.
- By presenting data-related risks, data locations, compliance frameworks, and the ongoing progress in addressing security concerns, Normalyze ensures better understanding and decision-making around security issues.
Safety Net
Risk Minimization
- The Normalyze single-pass scanner provides customers with greater confidence in their data security during mergers and acquisitions. The technology scans to identify sensitive data at rest and in motion without repeatedly exposing or removing data from its proper environment.
- By continuously monitoring and analyzing the data risk posture of the cloud environment, Normalyze helps customers understand which critical data assets are actually at risk and prioritize their security teams’ efforts in fixing these issues first.
Duty Roster
Reloaded
Tribal Knowledge
- In many cases, data security team members will be reassigned, resulting in a loss of tribal knowledge. Even though the team members from each of the merging companies typically have solid insights into their own data, they will likely be facing a lot of unknowns after the merger.
Think Strategically
Executive Communication
To communicate effectively, CISOs need to describe risk to other executives and the board in terms of its potential financial impact. Why? Because financial impact is the natural language of business leaders and clearly captures the consequence of risk to the organization. By showing in financial terms how security team actions result in reduced risk, CISOs demonstrate the value of their participation in the M&A process.
Normalyze’s monetary value of data calculation gives CISOs a real-world estimate of the cost a potential breach would incur to the organization. Monetary value is calculated based on publicly available data on the cost-to-handle per breached record, and can also be customized to the specific needs of the individual organization.
The monetary value of data provides CISOs with a strong argument to perform security and data hygiene due diligence early in the M&A process, so they can head off significant financial risk.