Data Access Governance
Find, classify, and restrict access to what matters most – your sensitive data
 ACCESS AUDIT
ACCESS AUDIT
Evaluate the complex cloud access control configuration – resource hierarchies, service account decision trees, IAM roles, individual resource level policies, etc. – to get a simple, accurate view of access privileges for all cloud data stores.
Continuously audit the access and privileges associated with data stores as well as other cloud resources. The key is that it’s automated, and Normalyze always gives you the current state.
 LEAST PRIVILEGE
LEAST PRIVILEGE
Restrict access to the minimum level required, which reduces the risk of data breaches. Achieve a more precise level of data access governance for users and internal and external resources.
DATA ACCESS
GOVERNANCE IN ACTION
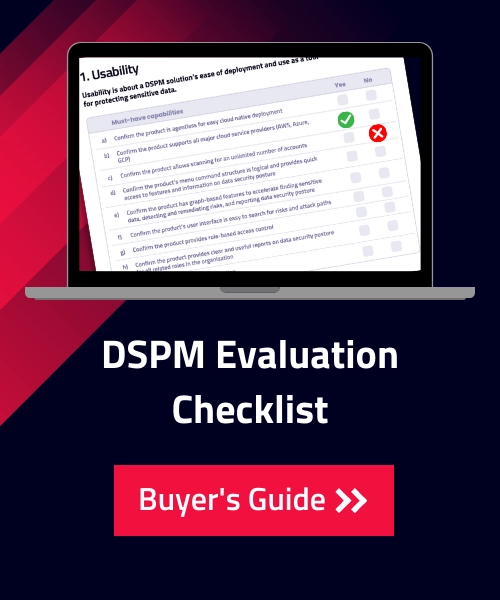
Eliminate blindspots in Snowflake data in three steps

|
Automated discovery and classification of all sensitive data using Normalyze’s one-pass data scanner, including custom data classes and hundreds of other data classes. |

|
Visualization using the Data Access Graph to identify role-based access and privileges granted to users to detect over-privileged users and tweak access policies. |
 |
Least Privilege enforcement through access adjustments is prioritized in support of remediating the most critical risks first. |
Visualize, Fix
Get a full picture of your sensitive data landscape and discuss your use case live with a security engineer.