In the past year, as we worked with many forward-looking CISOs and their sophisticated security teams, it has become clear that data proliferation is a huge problem across every company. Aside from the challenge of securing these data stores, the sheer volume of data stores makes it logistically hard for security teams to review every single one of the datastores discovered.
To address this challenge, Normalyze already provides ways for customers to cut through the clutter and focus on the most important areas, including classifying data stores by risk profile, categorizing data stores by type of data discovered, and filtering out risks associated with data stores by risk type and compliance tags.
Today, we’re providing another critical tool to help security teams in focusing their time and efforts on the most critical data vs. the long tail of data stores that exist in every company: the monetary value of sensitive data.
Monetary value of sensitive data
From the perspective of the boardroom as well as executive management, cybersecurity has traditionally been a risk management function. In recent years, accelerating digital transformation has made security play the role of business enabler. However, the risk management nature of the cybersecurity function hasn’t changed. Unlike traditional risk management in other domains, risk management in cybersecurity has not had a clear way to tie a monetary value to investments in products, people, processes, etc. Fines assessed via breach of compliance regulations are the closest we have in our industry.
Now, Normalyze is taking a unique approach – first in the DSPM category – to assess and associate a monetary value to every data store that is discovered and classified in the customer environment. With our platform’s comprehensive discovery and sensitive data classification capabilities, we already have full context of
- How much sensitive data exists in any given data store
- What type of data it is
- What type of risks are associated with the data store
- The likelihood of data breach resulting from these risks, and
- The potential impact of a breach
Synthesizing all of this together with a proprietary algorithm, we can now assess the monetary value of every data store we discover and classify.
Calculating monetary value
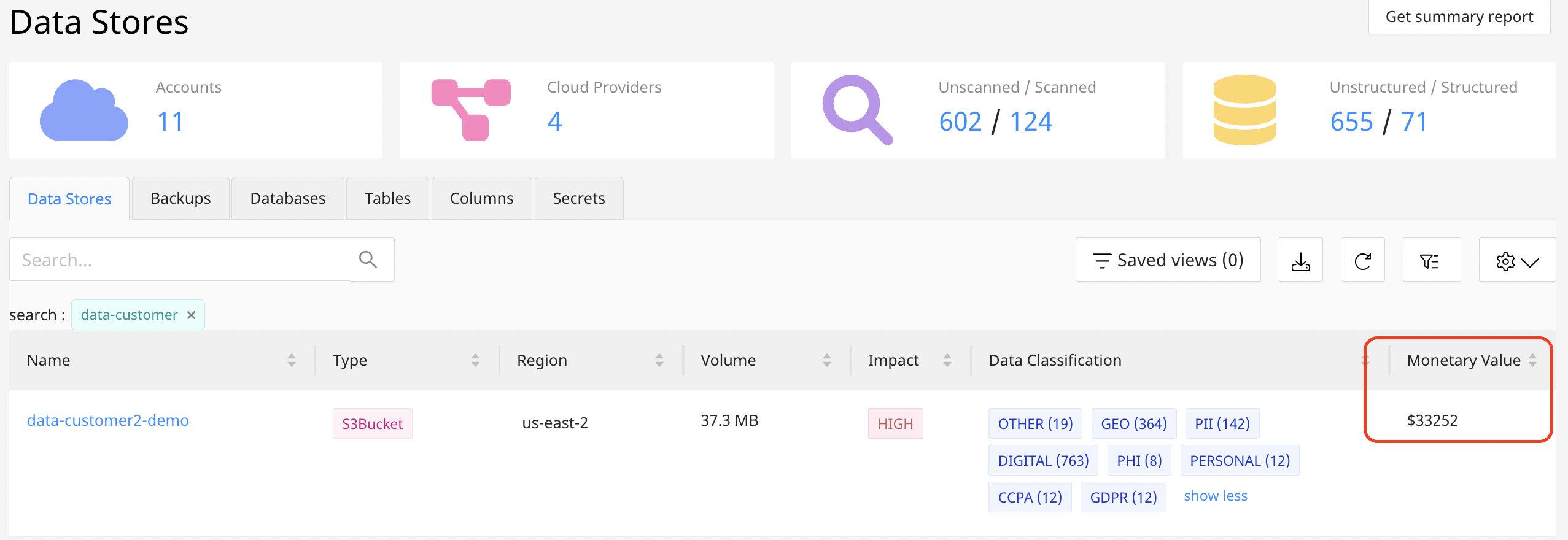
To clarify how it works, let’s walk through an example. The screenshot below from the Normalyze Platform shows the relevant risk attributes of a discovered S3 bucket named data-customer2-demo:
- What type of sensitive data it contains, e.g. social security numbers or patient records, and
- The amount of data, i.e. the number of sensitive records of each type discovered.
By multiplying the number of records of each type of sensitive data by the value of that record type (based on publicly available data on the cost-to-handle per breached record), Normalyze calculates the value of the data in this data store. Users are able to adjust the calculations based on their internal baselines or estimates.
The importance of these monetary value calculations is in their relative sizes. By looking at the monetary value of all of your data stores, security teams can quickly identify the sensitive data that has the highest monetary value to their organization and prioritize securing it.
Game-changing insight
This is a game-changing insight for security teams that helps them focus on the most valuable, impactful data store and work on minimizing the risk to that data. With monetary value assessed by Normalyze, there is finally a measurable ROI for data security teams!